Key Takeaway
The decentralized finance (DeFi) ecosystem faced its most significant security breach of 2026 on April 18, when Kelp DAO's cross-chain bridge was exploited for approximately $293 million in restaked ether (rsETH). This attack, attributed to North Korea's Lazarus Group, has sent shockwaves through the crypto industry, triggering emergency protocol freezes, exposing critical infrastructure vulnerabilities, and forcing Wall Street firms to reconsider their blockchain tokenization timelines. The incident represents more than just another hack - it highlights fundamental weaknesses in cross-chain bridge architecture that could determine whether institutional capital continues flowing into DeFi or retreats to traditional financial infrastructure.
The exploit's impact extends far beyond Kelp DAO itself. Major lending protocols including Aave, SparkLend, and Fluid were forced to freeze rsETH markets within hours, while the total value locked across DeFi protocols dropped by approximately $9 billion as spooked investors withdrew funds. Perhaps most significantly, investment bank Jefferies issued a warning that traditional financial institutions may temporarily slow their blockchain adoption initiatives as they reassess security risks. For investors navigating this volatile landscape, understanding the technical vulnerabilities, contagion risks, and broader implications of this exploit has become essential for making informed decisions about crypto exposure.
The Anatomy of the Kelp DAO Exploit
How the Attack Unfolded
The Kelp DAO exploit began at 17:35 UTC on April 18, 2026, when attackers successfully drained 116,500 rsETH tokens from the protocol's LayerZero-powered cross-chain bridge. At current prices, this represented roughly $292 million in value and constituted approximately 18% of rsETH's total circulating supply of 630,000 tokens. The attack exploited a critical vulnerability in the bridge's verification mechanism, which relied on a single-validator setup that LayerZero had previously warned against but Kelp had not addressed.
The technical mechanism was both sophisticated and alarming in its simplicity. Attackers manipulated LayerZero's cross-chain messaging protocol into believing legitimate instructions had arrived from another blockchain network, triggering Kelp's bridge to release the massive rsETH holdings to attacker-controlled addresses. LayerZero functions as infrastructure that enables different blockchains to send verified instructions to each other, and its OFT (Omnichain Fungible Token) standard was handling rsETH movement across more than 20 networks including Base, Arbitrum, Linea, Blast, Mantle, and Scroll.
Kelp DAO's emergency response team managed to pause the protocol's core contracts 46 minutes after the initial drain, at 18:21 UTC. However, two additional attack attempts occurred at 18:26 UTC and 18:28 UTC, each attempting to drain another 40,000 rsETH worth roughly $100 million. These follow-up attempts were successfully reverted thanks to the emergency pause, but the damage from the initial exploit had already been done.
The Lazarus Group Connection
Blockchain security firm LayerZero has attributed the Kelp DAO exploit to North Korea's Lazarus Group, specifically its TraderTraitor subunit known for targeting cryptocurrency and fintech companies. This attribution carries significant geopolitical implications, as North Korean hackers have stolen more than $2 billion in crypto in 2025 alone, with total crypto thefts since 2017 estimated at around $6 billion. These stolen funds are believed to help finance North Korea's weapons programs and circumvent international sanctions.
The Kelp DAO exploit follows a disturbingly similar pattern to the $285 million Drift Protocol hack that occurred on April 1, 2026, which was also linked to North Korean actors. In fact, the Kelp exploit now stands as the largest DeFi hack of 2026, slightly surpassing the Drift incident. The concentration of major attacks within such a short timeframe suggests that North Korean hacking operations have become increasingly sophisticated and well-resourced, posing a persistent threat to the entire crypto ecosystem.
The attack vector itself represents an evolution in Lazarus Group tactics. Rather than targeting smart contract vulnerabilities directly, the group exploited infrastructure weaknesses in cross-chain messaging layers - an approach that could be replicated against other protocols using similar bridge architectures. This shift toward targeting interoperability infrastructure rather than individual protocols raises the stakes for the entire DeFi industry.
Cross-Chain Bridge Vulnerabilities Exposed
The Single-Point-of-Failure Problem
The Kelp DAO exploit has thrown a harsh spotlight on the security trade-offs inherent in cross-chain bridge design. LayerZero placed responsibility for the exploit on Kelp's security configuration, noting that the liquid restaking protocol ran a single-verifier setup that the infrastructure provider had previously warned against. This revelation exposes a fundamental tension in DeFi infrastructure: the balance between operational efficiency and security decentralization.
Cross-chain bridges function as the connective tissue of the multi-chain ecosystem, enabling assets to move between Ethereum mainnet and various layer-2 networks. However, this interoperability comes at a cost. Bridges must verify that assets locked on one chain are legitimately represented on another, and this verification process requires trust assumptions. When protocols opt for single-validator or limited-validator setups to reduce costs and improve speed, they introduce centralization risks that sophisticated attackers can exploit.
The rsETH held in Kelp's bridge served as the reserve backing wrapped versions of the token deployed on every layer-2 blockchain. With that reserve drained, holders on non-Ethereum deployments now face the unsettling question of whether their tokens have any underlying value backing them. This creates a dangerous feedback loop where panic redemptions on layer-2 networks pressure the unaffected Ethereum supply, potentially forcing Kelp to unwind restaking positions to honor withdrawals - a process that could cascade through the entire liquid restaking ecosystem.
Systemic Risk Across DeFi
The Kelp exploit demonstrates how quickly problems in one protocol can spread throughout interconnected DeFi markets. Within hours of the attack, Aave froze rsETH markets on both V3 and V4, with founder Stani Kulechov clarifying that the exploit was external and Aave's contracts themselves were not compromised. Nevertheless, AAVE tokens fell approximately 10% as markets priced in potential bad debt exposure. The lending platform ultimately faced roughly $200 million in bad debt from the incident.
The contagion list continued to grow. SparkLend and Fluid followed Aave's lead in freezing their rsETH markets. Lido Finance paused further deposits into its earnETH product, which carries rsETH exposure, while emphasizing that its core stETH and wstETH staking protocols remained unaffected. Ethena temporarily paused its LayerZero OFT bridges from Ethereum mainnet as a precautionary measure, despite having no direct rsETH exposure and maintaining more than 101% overcollateralization.
This pattern of rapid protocol freezes and emergency pauses reveals the fragility of DeFi's interconnected architecture. Liquid restaking tokens like rsETH sit deep within the DeFi stack, accepted as collateral across multiple lending markets and integrated into numerous yield strategies. When the underlying security of these assets is compromised, the entire edifice of composed DeFi products faces stress testing. The $9 billion drop in total value locked across DeFi protocols following the exploit illustrates how quickly confidence can evaporate when fundamental infrastructure vulnerabilities are exposed.
Institutional Impact and Wall Street's Response
Jefferies Warns of Adoption Slowdown
Investment bank Jefferies issued a sobering analysis in the wake of the Kelp DAO exploit, suggesting that traditional financial institutions may temporarily slow their blockchain tokenization initiatives as they reassess security risks. Analyst Andrew Moss noted that TradFi tokenization initiatives are proliferating as institutional investment accelerates, but warned that the exploit and its cascading implications could temporarily slow TradFi adoption as security risks are re-evaluated.
This warning carries particular weight because major banks and asset managers have been accelerating efforts to tokenize traditional assets such as funds, bonds, and deposits. These tokenization efforts depend heavily on cross-chain infrastructure to move assets and maintain liquidity across platforms. Without secure bridges, Moss warned, markets could become fragmented, limiting the usefulness of tokenized assets and undermining the entire value proposition of blockchain-based financial instruments.
The timing of the Kelp exploit is especially problematic for institutional crypto adoption. Wall Street had been gradually warming to blockchain technology, with major firms announcing tokenization projects and exploring DeFi yield opportunities. The exploit exposes the gap between institutional-grade security expectations and the current state of DeFi infrastructure. For risk-averse institutional capital, the possibility of losing hundreds of millions to infrastructure vulnerabilities represents an unacceptable risk profile that could delay mainstream adoption by years.
The Security-Maturity Gap
The Kelp DAO incident highlights a fundamental challenge facing the crypto industry: infrastructure that is still maturing must support capital flows that increasingly resemble traditional finance in scale and sophistication. Jefferies' report explicitly noted that the nascent digital asset industry still requires time to mature, pointing to the need for more robust systems before tokenization can scale safely.
This maturity gap manifests in several ways. First, many DeFi protocols prioritize growth and user acquisition over security hardening, running validator setups that trade decentralization for efficiency. Second, the complexity of cross-chain interactions creates attack surfaces that are difficult to fully model and secure. Third, the rapid pace of innovation in DeFi means that infrastructure is often deployed before it has been battle-tested against sophisticated adversaries.
For institutional investors evaluating crypto exposure, the Kelp exploit serves as a reminder that DeFi remains an emerging technology with significant operational risks. While the long-term outlook for blockchain-based finance remains promising, the path to institutional adoption may require additional security infrastructure, insurance solutions, and regulatory frameworks that are still being developed. Protocols that can demonstrate institutional-grade security practices may find themselves at a competitive advantage as the industry matures.
Investor Takeaways and Risk Management
Navigating DeFi Security Risks
For individual investors, the Kelp DAO exploit offers several important lessons about managing crypto risk. First, diversification across protocols and chains can help mitigate exposure to any single point of failure. The investors most affected by the exploit were those with concentrated rsETH positions or heavy exposure to protocols that accepted rsETH as collateral. Spreading assets across multiple liquid staking and restaking solutions can reduce the impact of any single protocol failure.
Second, understanding the security assumptions underlying DeFi products is essential for informed investing. Cross-chain bridges, by their nature, require trust assumptions that pure layer-1 protocols do not. Investors should evaluate whether protocols use decentralized validator sets, have undergone comprehensive security audits, and maintain bug bounty programs. The single-validator setup that enabled the Kelp exploit was a known risk factor that more diligent investors might have identified.
Third, monitoring protocol health metrics can provide early warning signs of stress. Rising utilization rates in lending pools, declining total value locked, and unusual on-chain activity patterns can all signal emerging risks before they result in catastrophic losses. Tools that aggregate DeFi risk metrics and provide real-time monitoring capabilities have become essential infrastructure for sophisticated crypto investors.
Investors looking to identify high-quality DeFi protocols with robust security practices can leverage AI-powered screening tools to evaluate risk factors across multiple dimensions. By analyzing audit histories, validator decentralization, insurance coverage, and historical exploit data, these tools can help distinguish between protocols with institutional-grade security and those taking shortcuts that expose users to unnecessary risk.
The Case for Enhanced Due Diligence
The Kelp exploit demonstrates that even protocols with significant total value locked and apparent market traction can harbor critical vulnerabilities. Enhanced due diligence has become a necessity rather than a luxury for crypto investors. This due diligence should extend beyond reviewing smart contract audits to understanding the underlying infrastructure assumptions, cross-chain dependencies, and emergency response capabilities of protocols.
Investors should pay particular attention to how protocols handle cross-chain interactions, as these represent the most common attack vector for major exploits. Questions to ask include: What verification mechanisms secure bridge transactions? How many validators participate in cross-chain consensus? Has the bridge infrastructure been independently audited? What emergency pause mechanisms exist, and how quickly can they be activated?
The regulatory landscape around DeFi is also evolving rapidly, with implications for investor protection and protocol liability. As regulators develop frameworks for overseeing decentralized finance, protocols that proactively implement compliance measures and transparency standards may be better positioned for long-term survival. Investors should consider regulatory risk alongside technical risk when evaluating DeFi opportunities.
The Road Ahead for DeFi Security
Infrastructure Improvements on the Horizon
Despite the sobering lessons of the Kelp DAO exploit, the DeFi industry is not standing still. Multiple infrastructure improvements are being developed to address the vulnerabilities exposed by recent hacks. More robust cross-chain messaging protocols with decentralized validator sets are being deployed, offering stronger security guarantees than the single-validator setups that enabled the Kelp exploit. Insurance solutions for smart contract and bridge risk are maturing, providing investors with options for protecting their capital against protocol failures.
Zero-knowledge proof technology offers another promising avenue for improving cross-chain security. By enabling cryptographic verification of state transitions without revealing underlying data, zk-proofs could reduce the trust assumptions required for cross-chain bridges while maintaining the efficiency that makes bridges attractive in the first place. Several major bridge protocols are actively developing zk-based verification mechanisms.
The emergence of formal verification tools for smart contracts also represents progress toward more secure DeFi. These tools mathematically prove that contracts behave as intended under all possible conditions, eliminating entire classes of vulnerabilities that traditional auditing might miss. While formal verification remains computationally expensive and technically complex, it is gradually becoming more accessible for critical DeFi infrastructure.
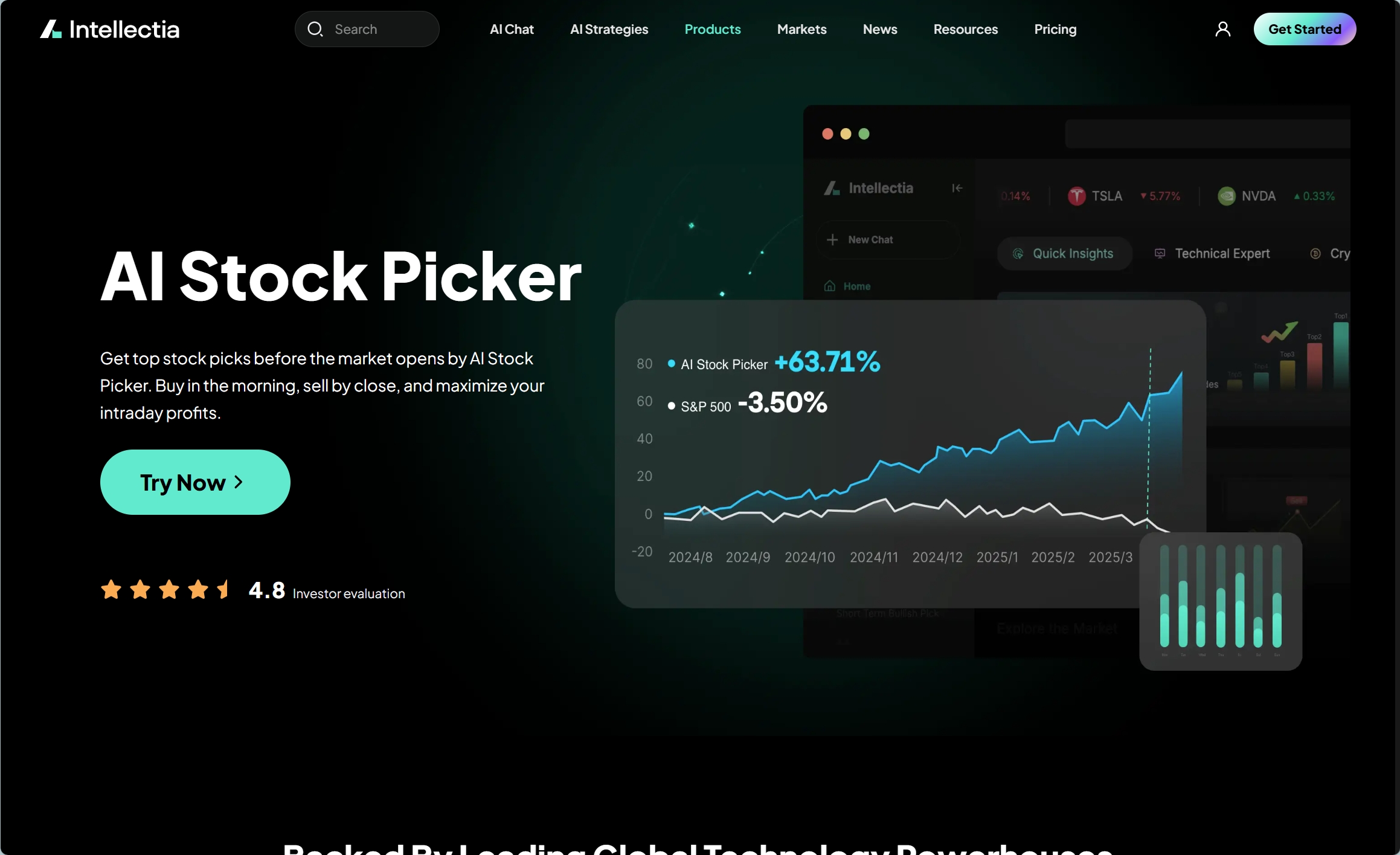
As DeFi security infrastructure evolves, investors can stay ahead of developments by using AI-powered stock and protocol pickers that incorporate security metrics into their analysis. These tools can identify protocols implementing cutting-edge security practices and flag those lagging behind industry standards, helping investors allocate capital toward the most resilient opportunities in the ecosystem.
Regulatory Response and Industry Standards
The concentration of major exploits in 2026 is likely to accelerate regulatory attention to DeFi security. Regulators in multiple jurisdictions have already expressed concerns about investor protection in decentralized finance, and high-profile hacks provide justification for more stringent oversight. The challenge for regulators will be developing frameworks that protect investors without stifling the innovation that makes DeFi valuable.
Industry self-regulation may also play a role in improving security standards. As institutional capital becomes more important for DeFi growth, protocols may voluntarily adopt security standards that exceed minimum regulatory requirements to attract sophisticated investors. Insurance providers and custodians can also drive security improvements by requiring protocols to meet specific criteria before offering coverage or custody services.
The DeFi community itself has demonstrated the ability to respond to security challenges. The rapid freezing of markets, coordinated emergency responses, and transparent communication following the Kelp exploit show that the industry has developed mechanisms for managing crises. Continued improvement of these response capabilities, combined with proactive security hardening, will be essential for rebuilding confidence after major incidents.
Conclusion
The $293 million Kelp DAO exploit represents a watershed moment for DeFi security in 2026. By exposing critical vulnerabilities in cross-chain bridge infrastructure and demonstrating how quickly problems can cascade through interconnected protocols, the hack has forced a reckoning for the entire industry. The attribution to North Korea's Lazarus Group adds geopolitical complexity, highlighting that DeFi security is not merely a technical challenge but a matter of national security and international finance.
For investors, the Kelp exploit serves as a powerful reminder that crypto investing requires sophisticated risk management and thorough due diligence. The protocols that survive and thrive in the coming years will likely be those that treat security as a fundamental design principle rather than an afterthought. Cross-chain infrastructure will need to evolve rapidly to meet institutional security standards, and the gap between DeFi's current capabilities and traditional finance's expectations will need to narrow significantly.
Looking ahead, the long-term trajectory of DeFi remains promising despite these setbacks. The fundamental value proposition of decentralized financial infrastructure - enabling programmable, transparent, and efficient financial services without traditional intermediaries - remains compelling. However, the path to realizing this vision requires continued investment in security infrastructure, regulatory clarity, and industry standards that can support institutional-scale capital flows. Investors who can navigate these challenges while identifying protocols with genuine security advantages may find exceptional opportunities as the industry matures.
Ready to navigate DeFi's evolving security landscape with confidence? Sign up for Intellectia.ai today and access AI-powered tools that analyze protocol security, identify emerging risks, and help you build resilient crypto portfolios. Our platform combines on-chain analytics with machine learning to surface insights that can protect your capital while capturing DeFi's upside potential.





