Key Takeaway
The quantum threat to Bitcoin just became significantly more tangible. On April 24, 2026, independent researcher Giancarlo Lelli successfully broke a 15-bit elliptic curve cryptography key using publicly accessible quantum hardware, winning a 1 Bitcoin bounty from quantum security firm Project Eleven. While this represents a 512-fold improvement over the previous public demonstration from September 2025, it is important to maintain perspective: Bitcoin uses 256-bit encryption, making the actual network still far from vulnerable. However, the acceleration in quantum capabilities signals that Q-Day, the moment when quantum computers can compromise Bitcoin's core security, may arrive sooner than many previously anticipated.
This development arrives amid heightened urgency from multiple credible sources. Google researchers recently published findings suggesting that a sufficiently powerful quantum computer could crack Bitcoin's core cryptography in under nine minutes, with some analysts predicting such capabilities could emerge as early as 2029. With over 6.5 million Bitcoin tokens (worth hundreds of billions of dollars) sitting in addresses that quantum computers could theoretically target, the stakes could not be higher. The crypto industry now faces a race against time to implement post-quantum cryptographic defenses before the threat materializes.
Stay ahead of emerging crypto threats with Intellectia's AI-powered screening tools. Our platform continuously monitors security developments and market conditions across the cryptocurrency landscape, helping you make informed decisions in an evolving threat environment.
Understanding the Quantum Threat to Bitcoin
How Elliptic Curve Cryptography Secures Bitcoin
Bitcoin's security foundation rests on a one-way mathematical relationship that has protected the network since its inception. When you create a Bitcoin wallet, the system generates a private key, a secret number that must never be shared, and derives a corresponding public key from it using elliptic curve cryptography (ECC), specifically the secp256k1 curve. This public key can be freely distributed and is visible on the blockchain whenever you receive funds.
The genius of this system lies in its asymmetry. While deriving a public key from a private key is computationally trivial, reversing the process, figuring out the private key from the public key, is supposed to be practically impossible. Modern classical computers would require billions of years to break this encryption through brute force, making Bitcoin's security computationally impossible to compromise using current technology.
When you spend Bitcoin, you do not reveal your private key. Instead, you use it to generate a cryptographic signature that proves ownership without exposing the secret itself. The network can verify this signature using only your public key, confirming that you control the funds without ever learning your private key. This elegant system has secured hundreds of billions of dollars in value for over fifteen years.
Why Quantum Computers Change Everything
Quantum computers operate on fundamentally different principles than classical computers. While classical computers process information in binary bits (0s and 1s), quantum computers use quantum bits or qubits, which can exist in multiple states simultaneously thanks to quantum superposition. This property enables quantum computers to perform certain calculations exponentially faster than any classical computer ever could.
The specific threat to Bitcoin comes from Shor's algorithm, developed by mathematician Peter Shor in 1994. This quantum algorithm can factor large numbers and solve discrete logarithm problems exponentially faster than classical algorithms, the exact mathematical problems that underpin Bitcoin's elliptic curve cryptography. A sufficiently powerful quantum computer running Shor's algorithm could theoretically derive private keys from public keys, completely compromising the security of exposed addresses.
Google's recent research sent shockwaves through the crypto community by suggesting that a cryptographically relevant quantum computer could crack Bitcoin's core cryptography in under nine minutes, faster than the average Bitcoin block settlement time. This is not science fiction; it is a mathematical reality that becomes more concerning with each quantum computing breakthrough.
The 15-Bit Breakthrough: What Giancarlo Lelli Achieved
A 512-Fold Leap in Quantum Attack Capability
The latest quantum breakthrough comes from Italian researcher Giancarlo Lelli, who spent a full year working on the challenge. Using publicly accessible quantum hardware, Lelli successfully broke a 15-bit elliptic curve key, a feat that represents a 512-fold improvement over the previous public demonstration achieved in September 2025.
To put this in perspective, a 15-bit key has a search space of 32,767 possible combinations. While this is microscopic compared to Bitcoin's 256-bit security, the rate of improvement is what is concerning. The jump from previous demonstrations to this latest achievement shows that quantum attack capabilities are advancing rapidly, and each milestone brings the theoretical threat closer to reality.
Project Eleven CEO Alex Pruden said: We are still far, objectively, from the point at which you could actually break Bitcoin. But how long will it take to close that gap, and will we know the closer we get? This uncertainty, whether we will see the threat coming with enough warning, adds urgency to preparation efforts.
The Q-Day Prize and Its Significance
Project Eleven, a quantum security startup, established the Q-Day Prize as a bounty program designed to accelerate quantum attack research and raise awareness about the growing threat to cryptographic systems. The prize awarded to Lelli, 1 Bitcoin worth approximately $78,000 at current prices, represents both an acknowledgment of his achievement and a warning to the broader crypto industry.
The Q-Day Prize serves a dual purpose. First, it incentivizes researchers to push the boundaries of what is possible with current quantum hardware, helping the industry understand where the threat actually stands rather than relying on theoretical projections. Second, it maintains public awareness that quantum computing poses a real, existential threat to current cryptographic standards, not a hypothetical concern for some distant future.
The Timeline: When Could Quantum Computers Threaten Bitcoin?
Google's Alarming Projection: 2029
Google's recent research paper on quantum vulnerabilities in cryptocurrency sent ripples through both the tech and crypto communities. Their analysis suggests that the quantum threat to Bitcoin could materialize as early as 2029, a timeline that does not leave much room for complacency. The research indicates that future quantum computers may break elliptic curve cryptography with fewer qubits and gates than previously realized, potentially accelerating the timeline beyond earlier estimates.
The implications of this timeline are profound. If Google is correct, the crypto industry has less than three years to implement and deploy post-quantum cryptographic solutions across Bitcoin and other major blockchains. Given the complexity of blockchain upgrades and the conservative nature of Bitcoin development, this represents an extremely tight window.
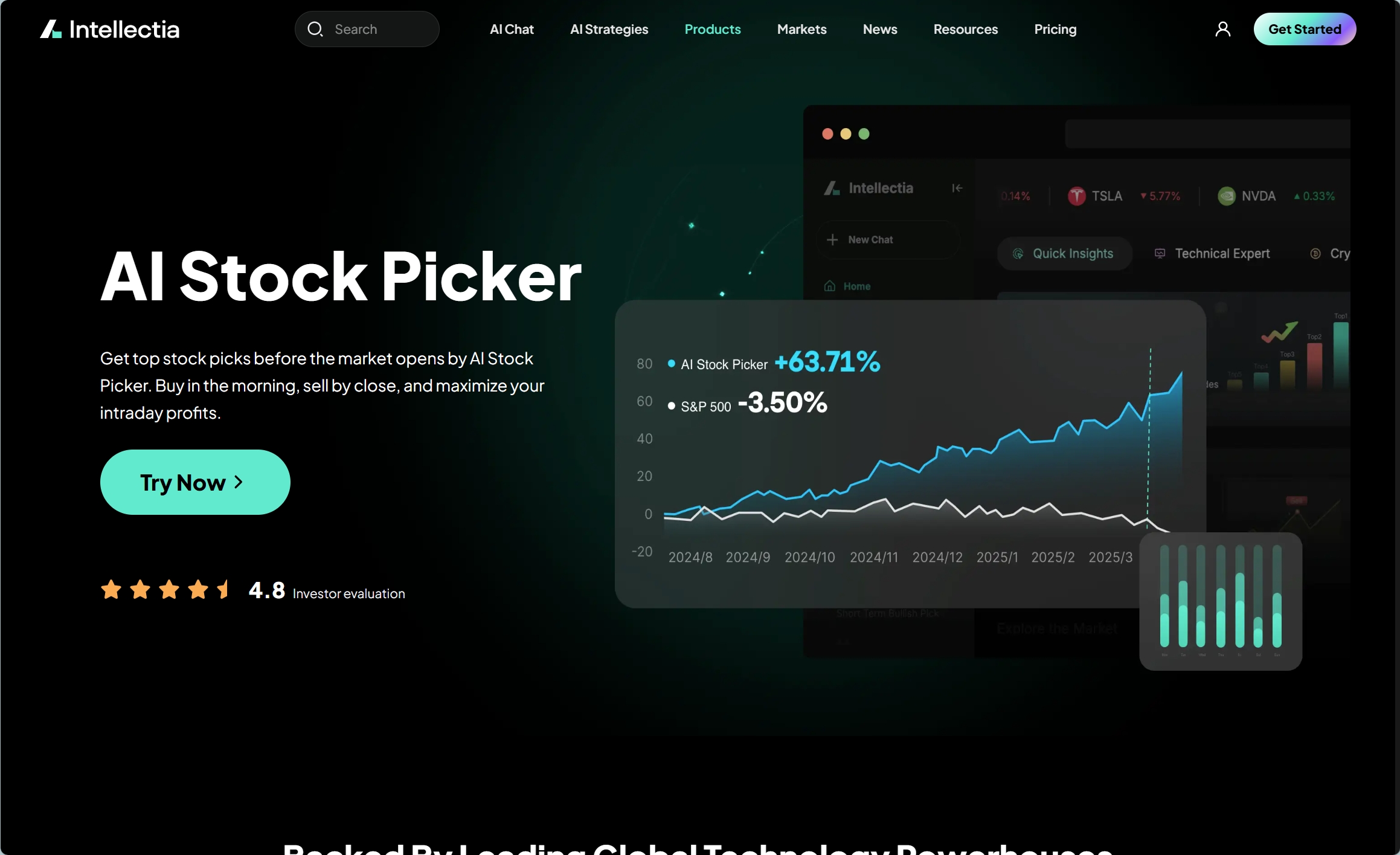
Navigate volatile crypto markets with confidence using Intellectia's AI Stock Picker. Our AI analyzes market conditions, security developments, and technical indicators to help you build resilient portfolios in an uncertain landscape.
Bernstein's More Conservative View: 3-5 Years
Wall Street broker Bernstein offered a slightly more conservative but still urgent timeline in a recent analysis. According to their research, Bitcoin and the broader crypto ecosystem have a three to five-year window to transition to post-quantum security through protocol upgrades and wallet changes. They characterize the quantum threat as real, but manageable, provided the industry takes action sooner rather than later.
Bernstein's analysis also identified that the risk is not evenly distributed across the Bitcoin network. Older wallets, particularly those belonging to early adopters who have not moved their coins in years, face the greatest exposure. This includes coins held by Bitcoin's pseudonymous creator, Satoshi Nakamoto, estimated to be worth tens of billions of dollars. Core network functions like mining remain largely secure even in a post-quantum world, but the vulnerability of legacy addresses poses a significant challenge.
Vulnerable Bitcoin: The $400 Billion at Risk
The 6.5 Million Bitcoin Problem
Approximately 6.5 million Bitcoin tokens, worth roughly $400-500 billion at current prices, sit in addresses that quantum computers could directly target. These are not necessarily lost or abandoned coins; many belong to early adopters who simply have not moved their holdings in years, either out of conviction, lost access, or strategic patience.
The quantum vulnerability specifically affects addresses where the public key has been exposed on the blockchain. This happens whenever you send Bitcoin from an address, the transaction reveals the public key needed to verify the signature. Addresses that have only received funds but never sent them (unspent transaction outputs, or UTXOs) do not expose their public keys and remain safe from quantum attacks, at least until they are spent.
This creates a counterintuitive security dynamic: the most dormant Bitcoin, coins that have not moved in years, is paradoxically the most vulnerable to quantum attacks. Early miners and adopters who accumulated large positions in Bitcoin's early days and have not touched them since face the highest risk. Satoshi Nakamoto's estimated holdings alone represent a significant portion of this vulnerable supply.
The Satoshi Nakamoto Question
The potential compromise of Satoshi Nakamoto's coins represents more than just a financial loss, it would strike at Bitcoin's core mythology and credibility. Satoshi's estimated holdings of approximately 1 million Bitcoin, worth over $75 billion at current prices, have never moved from their original addresses. These coins serve as a symbol of Bitcoin's decentralized origins and the creator's commitment to the project's principles.
If quantum computers eventually crack the private keys controlling these addresses, the resulting coins could flood the market, causing massive price disruption. Alternatively, the mere possibility that someone might possess Satoshi's keys could introduce uncertainty that affects market sentiment. The crypto community has debated whether steps should be taken to freeze these legacy addresses through protocol changes, though such moves raise significant philosophical questions about Bitcoin's immutability and censorship resistance.
Post-Quantum Solutions: Protecting Bitcoin's Future
BIP 360: Pay-to-Merkle-Root (P2MR)
Bitcoin developers are not sitting idle in the face of this emerging threat. One of the most prominent proposals for quantum-proofing Bitcoin is BIP 360, titled Pay-to-Merkle-Root. This proposal aims to upgrade Bitcoin's underlying cryptographic primitives to use post-quantum algorithms like Dilithium, ensuring the network remains secure even against attacks from cryptographically relevant quantum computers.
BIP 360 represents a significant architectural change to how Bitcoin addresses work. The proposal would introduce a new address type that uses Merkle tree structures combined with post-quantum signature schemes. This approach maintains backward compatibility while providing a migration path to quantum-resistant security. However, implementing such changes requires broad consensus among Bitcoin developers, miners, and users, a notoriously difficult achievement in Bitcoin's decentralized ecosystem.
BIP 361: The Migration Plan
Jameson Lopp, a prominent Bitcoin cypherpunk and security expert, along with five co-authors, published BIP 361 titled Post Quantum Migration and Legacy Signature Sunset. This draft proposal outlines a three-phase plan to push users toward quantum-resistant addresses while addressing the challenge of legacy coins that may never be moved.
BIP 361's approach is more aggressive than BIP 360, proposing mechanisms to eventually sunset legacy signature schemes that remain vulnerable to quantum attacks. The proposal has sparked significant debate within the Bitcoin community, particularly around questions of whether the protocol should take steps that could effectively freeze coins held in vulnerable addresses. This touches on fundamental questions about property rights, immutability, and the social contract of Bitcoin.
Hash-Based Signatures: SPHINCS+ and Lamport
Beyond the BIP proposals, researchers are exploring various post-quantum signature schemes that could replace or supplement Bitcoin's current elliptic curve signatures. Hash-based signatures like SPHINCS+ (SPHINCS Plus) and Lamport signatures offer promising quantum resistance because their security relies on the properties of hash functions rather than discrete logarithm problems.
Hash functions are believed to be more resistant to quantum attacks than elliptic curve cryptography. While Grover's algorithm (another quantum algorithm) can provide a speedup for brute-forcing hash functions, the improvement is quadratic rather than exponential, meaning hash-based cryptography remains viable in a post-quantum world, albeit with larger key sizes.
The trade-off is significant: post-quantum signatures can be tens to hundreds of times larger than current ECDSA signatures. This dramatic size increase could severely impact blockchain scalability, increasing storage requirements, bandwidth usage, and transaction fees. The Coinbase advisory board highlighted this challenge, noting that the transition to post-quantum cryptography is not a simple swap but a complex engineering problem with real economic consequences.
Industry Response and Preparation
Google's Post-Quantum Timeline
Google is not just researching the quantum threat, they are actively preparing for it. In March 2026, Google published a formal timeline to transition its entire infrastructure to post-quantum cryptography by 2029. This corporate commitment provides a useful benchmark for the broader tech industry and validates the urgency of preparing for quantum capabilities.
Google's timeline includes transitioning internal systems, updating external APIs, and ensuring all Google services use quantum-resistant encryption by their target date. For the crypto industry, Google's commitment signals that major technology players view the quantum threat as imminent rather than theoretical.
The Coinbase Advisory Board Warning
Coinbase, one of the largest cryptocurrency exchanges in the world, has taken a proactive stance on quantum preparedness. Their advisory board recently issued a warning that the quantum computing threat is on the horizon and that the crypto industry needs a concrete plan for addressing it. This warning from a major institutional player adds credibility to concerns that might otherwise be dismissed as alarmist.
The advisory board emphasized the practical challenges of transitioning to post-quantum cryptography, particularly the signature size problem. They noted that post-quantum digital signatures can be tens to hundreds of times larger than current ones, which could dramatically increase blockchain data costs and reduce network throughput.
Protect your investments in uncertain times. Sign up for Intellectia to access advanced analytics, security monitoring, and AI-powered insights that help you navigate the evolving crypto landscape with confidence.
What This Means for Bitcoin Investors
Near-Term Security: No Immediate Panic
For Bitcoin holders, the most important message is that there is no immediate cause for panic. The 15-bit key broken by Giancarlo Lelli is still 241 bits smaller than Bitcoin's 256-bit security. The gap between current quantum capabilities and what is needed to threaten Bitcoin remains enormous, so large that even exponential improvements in quantum technology will not close it overnight.
Bitcoin's current security model remains intact, and the network continues to process transactions securely. The quantum threat is real and growing, but it is not an imminent danger that should cause investors to abandon their holdings or make drastic changes to their strategies.
Long-Term Considerations
However, the quantum threat should factor into long-term investment thinking, particularly for holders of significant Bitcoin positions. The industry is moving toward post-quantum solutions, but the transition will take time and may involve disruptions. Investors should stay informed about developments in quantum computing and the various proposals for protecting Bitcoin against these threats.
One practical consideration: if you hold Bitcoin in addresses that have never sent funds (and therefore have not exposed their public keys), your holdings remain safe from quantum attacks regardless of computing advances. Only when you spend from an address does it become vulnerable. This creates an interesting security dynamic where HODLing (holding long-term without moving coins) actually provides quantum protection.
The Broader Implications for Cryptocurrency
Beyond Bitcoin: Ethereum and Altcoins
While Bitcoin receives the most attention, the quantum threat extends to virtually all major cryptocurrencies. Ethereum, the second-largest blockchain by market capitalization, also relies on elliptic curve cryptography for transaction signing and smart contract security. Many altcoins use similar or identical cryptographic primitives, making them equally vulnerable to quantum attacks.
The Ethereum community has also been exploring post-quantum solutions, though Ethereum's more flexible upgrade path (compared to Bitcoin's conservative approach) may allow for faster implementation of protective measures. Other blockchain projects, particularly newer ones, are already building quantum resistance into their protocols from the ground up.
The Race Between Quantum and Post-Quantum
We are witnessing a race between two exponential trends: the advancement of quantum computing capabilities and the development of post-quantum cryptographic solutions. The April 2026 breakthrough demonstrates that quantum computing is advancing faster than many expected, but the crypto industry is also mobilizing with unprecedented urgency.
The outcome of this race will shape the future of digital finance. If post-quantum solutions can be widely deployed before cryptographically relevant quantum computers emerge, Bitcoin and other cryptocurrencies can emerge stronger than ever.
Conclusion
The quantum threat to Bitcoin has transitioned from theoretical concern to tangible reality. Giancarlo Lelli's breakthrough in breaking a 15-bit elliptic curve key using publicly accessible quantum hardware serves as a wake-up call for the entire cryptocurrency industry. While Bitcoin's 256-bit security remains far beyond current quantum capabilities, the pace of advancement suggests that complacency is no longer an option.
With Google projecting cryptographically relevant quantum computers by 2029 and hundreds of billions of dollars in Bitcoin potentially at risk, the industry faces its most significant security challenge since the network's inception. The good news is that developers are actively working on solutions, from BIP 360 and BIP 361 to alternative post-quantum signature schemes.
For investors, the key takeaway is vigilance without panic. Bitcoin remains secure today, and the quantum threat, while real, is still years away from materializing. However, this is precisely the time to stay informed, understand the risks, and support the development of quantum-resistant solutions.
Ready to stay ahead of the curve? Try Intellectia's premium features to access real-time security monitoring, advanced portfolio analytics, and AI-powered insights that help you navigate the complex intersection of quantum computing and cryptocurrency. The future belongs to those who prepare for it today.





